Unauthenticated RSFTP to Command Injection
A blog post about priority one bug submitted to a private program on Bugcrowd which would have allowed a malicious unauthenticated user to fully compromise a customer's server.
Read moreWe munch on code. Your code. It's good for us, it's good for you.
Is your corporate network safe against an internal attacker?
Find out moreAre your website and your users' data protected against a malicious hacker's attack?
Find out moreMobile Applications are like web applications but have introduced a new set of vulnerabilities.
Find out moreIOT devices are becoming more popular in our everyday life. Malicious actors are turning their attention towards smart devices potentially affecting millions of users.
Find out moreYou have decided to run a bug bounty program but you have never had a penetration test before. We might have the right solution for you.
Find out moreAre your employees the weak link in the chain?
Find out moreCodeGrazer is the Pentest firm made for you. Here is why:
High quality testing. Work with one of the best pentesters and bug hunters!
Quotes in 24/h. Let us know what you want to test and we will send you a quote in a working day.
Tailored prices. Prices can be tailored to your needs. Startup packages are available!
Quick reporting. Reporting is the most important part of a pentest. We will deliver a high quality report in max. 2 working days.
Free web app retests. You want to make sure you fixed that SQL injection we found? We can do that for you free of charges.



A blog post about priority one bug submitted to a private program on Bugcrowd which would have allowed a malicious unauthenticated user to fully compromise a customer's server.
Read more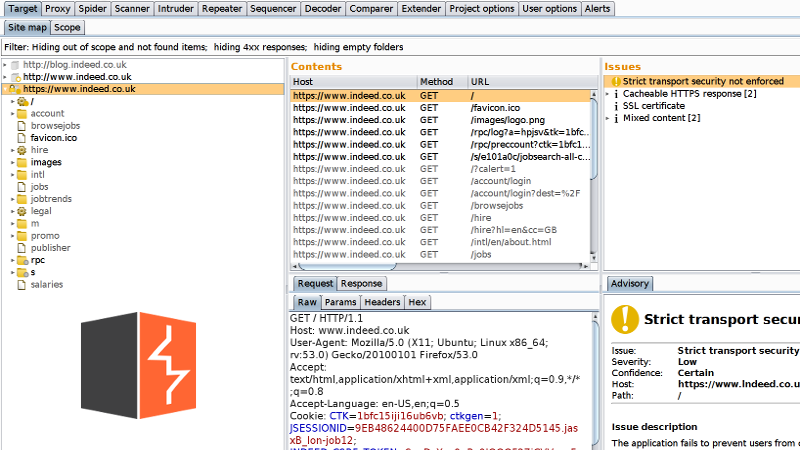
A tutorial written as an introduction to Burp Suite, explaining how to install and use Burp Suite, fundamental tool used by bug hunters and pentesters on daily basis to test web applications.
Read more
Starting in October the 11th, @_dc151 started running a social event with lightning talks related to hacking. For the second event held on 8th of November, I was asked to talk about my experience with bug bounties. Since it is a wide and interesting topic, I decided to start from the beginning and address some questions a beginner would have regarding the topic.
Read more
This blog post shows examples of reflected cross-site scripting that I found in the past few years while hunting for bugs for private customers and bug bounty programs.
Read more
My first blog post will talk about a security vulnerability that I discovered, a very simple username enumeration vulnerability with a lot of potential for damage.
Read more